Cryptographic authentication represents the most significant advancement in digital security since the internet became public. This technology uses mathematical algorithms to verify your identity without revealing passwords or personal details. Think of it as mathematical proof that you are who you claim to be.
Traditional password-based systems have become dangerously vulnerable to modern attacks. The Verizon Data Breach Investigations Report 2025 confirmed that the human element is implicated in roughly 60% of all breaches worldwide. Organizations are finally responding with urgency. According to Okta’s Secure Sign-in Trends Report 2025, phishing-resistant authenticators using public key cryptography have experienced unprecedented adoption. FastPass adoption nearly doubled from 6.7% to 13.3% in just one year. More impressively, 61% of organizations surveyed in the RSA ID IQ Report 2025 have committed to rolling out passwordless cryptographic authentication within the next twelve months.
Understanding Cryptographic Authentication: The Basics
How Cryptographic Authentication Works
Cryptographic authentication depends on two mathematically linked keys that cannot be derived from each other. Your public key functions like a mailbox anyone can access. Your private key is the only key that opens it. When you log in, the server uses your public key to create a mathematical challenge. Only your private key can solve it correctly. If verified, you’re authenticated.
This process happens through mathematical functions that are computationally infeasible to reverse. No passwords are transmitted. Pure mathematics proves you possess the private key and therefore are who you claim to be. Even if attackers obtain your public key, they cannot solve the mathematical challenge without your private key.
Why Public Key Cryptography Changed Security Forever
Before 1975, every encryption system used a single shared secret key for both encoding and decoding. Managing these secrets across millions of users became logistically impossible. Public key cryptography solved this with an elegant insight: use two mathematically linked but non-derivable keys. Your public key can be shared freely across the internet. Your private key remains secure with you alone. This one-way relationship made digital authentication practical for billions of people.
The three most common public key algorithms are RSA, Elliptic Curve Cryptography (ECC), and Digital Signature Algorithm (DSA). Each uses different mathematical approaches to link keys without making them reversible.
HOW CRYPTOGRAPHIC AUTHENTICATION WORKS: 5-STEP PROCESS?
Digital Signatures: Proving Authorship
Digital signatures provide absolute proof that you created or authorized something. You sign with your private key creating a unique signature. Recipients verify using your public key. Mathematics guarantee only your private key could create that signature. Digital signatures prove authentication, integrity, and non-repudiation simultaneously.
Code signing represents a critical 2025 application. According to the Encryption Consulting Global Encryption Trends 2025 Report, 54% of organizations implemented code-signing by 2024, with 87% planning expansion in 2025. The damaging AnyDesk cyberattack in 2024, where compromised code-signing certificates allowed malicious code signing, accelerated this adoption.
Certificate-Based Authentication
Digital certificates function like government ID cards for the internet. They contain your public key and identity information. A Certificate Authority digitally signs your certificate using their private key, proving the public key belongs to you. This prevents attackers from using fake keys to impersonate legitimate websites.
Zero-Knowledge Proofs: Proving Without Revealing
Zero-knowledge proofs prove something is true without revealing underlying information. Imagine proving you’re older than eighteen without showing your birth certificate. With zero-knowledge proofs, you prove your age without revealing exact birth date, address, or identity. The mathematics guarantee validity while protecting privacy completely.
According to TechScience research (December 2025), zero-knowledge proof-based identification systems now provide complete GDPR and NIST compliance. Ghana’s national identification system has pioneered ZKP implementation, enabling citizens to verify critical attributes like age without disclosing sensitive information. The Zero-Knowledge KYC market is projected to grow from $83.6 million in 2025 to $903.5 million by 2032—an average annual growth rate exceeding 40%.
End-to-End Encryption and Implementation Challenges
What End-to-End Encryption Accomplishes
End-to-end encryption ensures data remains encrypted during its entire journey from sender to recipient. Your device encrypts messages before sending them. No server, intermediary, or internet service provider can decrypt your messages. Only the recipient’s device can decrypt using their private key.
This prevents even the service provider from accessing your data. WhatsApp, Signal, and Apple iMessage cannot read your messages themselves. Neither can governments with subpoenas nor hackers who compromise servers. Messages remain mathematically protected throughout their journey.
Real Implementation Challenges
Implementing end-to-end encryption creates substantial complexity. Key management becomes critical—organizations must securely generate, store, rotate, and retire cryptographic keys. Losing your key means losing access to encrypted data permanently with no recovery.
Recovery procedures create friction when users lose authenticator devices. These usability challenges slow adoption significantly. Additionally, cryptographic operations consume processor power and battery life, requiring optimized implementations for performance.
Zero-Trust Architecture: Continuous Cryptographic Authentication
Continuous Verification Instead of One-Time Authentication
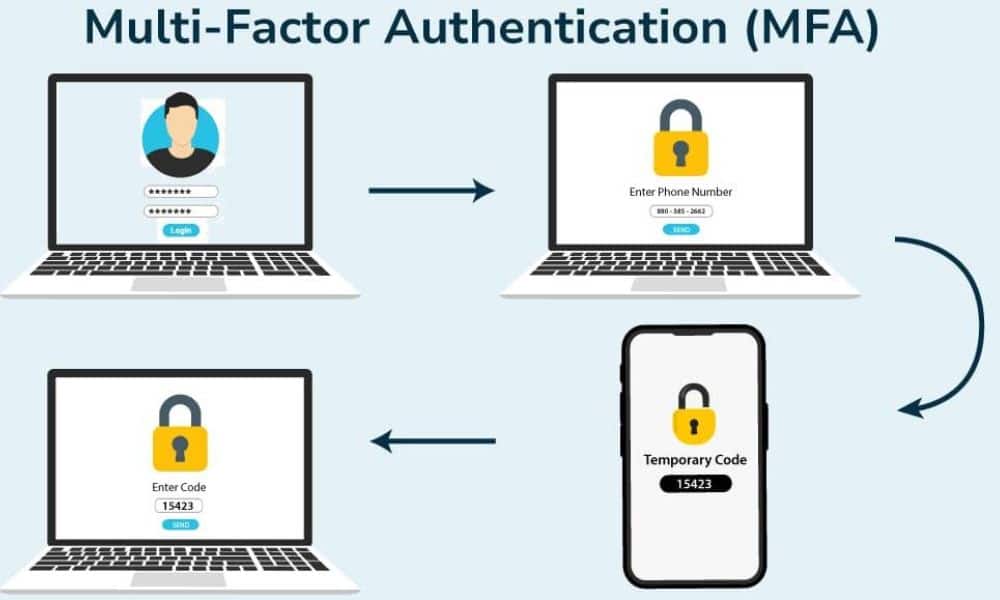
Traditional security models verified identity once during login, then trusted the entire session. Zero-trust architecture requires continuous verification throughout every interaction. Every action triggers new cryptographic verification automatically.
In zero-trust systems, you authenticate to access email, then re-authenticate to download a file, then re-authenticate when accessing different folders. Each action requires new cryptographic proof. If credentials change or unusual activity appears, access stops immediately.
This approach eliminates dangerous vulnerability windows after initial authentication. In 2024, most breaches occurred after attackers gained legitimate credentials through phishing. Continuous cryptographic authentication makes this far more difficult to exploit because each transaction requires new cryptographic proof.
Leading financial institutions and healthcare organizations deploy zero-trust with continuous cryptographic authentication to protect assets and patient data. Behavioral monitoring works alongside cryptographic authentication—unusual locations or changed patterns trigger additional verification.
Cryptographic Authentication vs. Passwords
Why Passwords Fail
One critical vulnerability is SIM swap attacks, where criminals intercept SMS
codes used for two-factor authentication. The Anatomy of a SIM Swap Attack: How
Hackers Steal Your Identity demonstrates how attackers exploit phone number
hijacking to compromise accounts that rely on password-plus-SMS security. This
is why cryptographic authentication with hardware keys eliminates this
vulnerability entirely.
Passwords depend on human memory and behavior, creating inherent problems. People choose weak passwords they remember, reuse them across websites, and write them in notebooks. One person’s weakness compromises security everywhere.
Password databases can be cracked offline. Attackers steal entire databases and systematically break hashes. A stolen database from 2010 can still compromise accounts in 2025 if passwords haven’t changed.
Passwords are vulnerable to phishing. Users cannot distinguish real login pages from fake ones. Convincing phishing emails steal passwords before any security system protects users. The RSA ID IQ Report 2025 confirmed credential abuse remains the primary attack vector. Small and medium-sized businesses are hardest hit, with ransomware in 88% of breaches.
In one 2025 incident, Sygnia responders observed sophisticated identity-based attacks starting with LinkedIn and WhatsApp social engineering. Attackers convinced development staff to download code, harvesting credentials from corporate laptops.
Cryptographic authentication makes phishing attacks mathematically impossible. Even if you submit credentials to fake websites, authentication fails—the fake site cannot complete the mathematical challenge without your private key. You’re never authenticated regardless of submitted credentials.
Cryptographic keys cannot be stolen through phishing. Your private key never leaves your device. Without your private key, attackers cannot impersonate you mathematically. Cryptographic authentication scales infinitely across all accounts. You use the same key pair everywhere, never reusing passwords. Mathematics prevent credential reuse attacks absolutely.
According to Okta’s 2025 analysis, password usage declined from 95.1% to 93.0% of total authentication methods. More significantly, 7% of enterprise users eliminated passwords entirely, demonstrating that enterprise-scale password elimination is achievable today.
NIST Post-Quantum Cryptography Standards
Three Quantum-Resistant Algorithms Available Now
On August 13, 2024, NIST released the first three Post-Quantum Cryptography standards. These represent the foundation for quantum-safe cryptographic authentication before quantum computers become available.
- ML-KEM (FIPS 203) provides quantum-resistant key agreement that is production-ready today. Organizations should deploy ML-KEM immediately as their primary key exchange mechanism. AWS began deploying ML-KEM-768 hybrid key exchange in December 2024. Cloudflare has protected 16% of internet traffic using ML-KEM hybrid key exchange.
- ML-DSA (FIPS 204) provides quantum-resistant digital signatures. It’s designed for document signing, authentication certificates, and code signing. First ML-DSA certificates are expected in 2026.
- SLH-DSA (FIPS 205) provides quantum attack defense using hash-based cryptography. Unlike ML-DSA, SLH-DSA requires no trusted setup.
The Quantum Threat and HNDL Attacks
NIST experts acknowledge RSA encryption could become vulnerable to quantum computers by 2030. “Harvest Now, Decrypt Later” attacks are already occurring. Adversaries systematically collect encrypted data today to decrypt later once quantum computers become available.
Organizations must transition to quantum-resistant cryptography before 2030 to protect long-term data confidentiality. Under NIST’s transition timeline in IR 8547, NIST will deprecate quantum-vulnerable algorithms by 2035. High-risk systems must transition much earlier.
Real-World Applications: Where Cryptographic Authentication Works
Government, Finance, and Healthcare
Governments deploy cryptographic authentication for classified communications. The U.S. Department of Defense requires cryptographic authentication for all IT systems. Military personnel carry cryptographic smartcards for access control.
Banks implement cryptographic authentication through chip reader cards and biometric systems. Cryptocurrency exchanges depend entirely on cryptographic authentication. According to banking case studies, Standard Chartered Bank’s cryptographic authentication prevented attacker access to passwords and PINs despite database breach. Attackers stole 2 GB of customer data but could not crack encrypted credentials.
Electronic health record systems protect sensitive medical information using cryptographic authentication. A healthcare consortium piloted the Mina Protocol for patient identity verification across hospital systems. Healthcare providers verified patients met specific criteria without accessing complete medical records.
Healthcare and Voting Innovations
Estonia has deployed zero-knowledge proof voting systems, enabling voters to vote from home while maintaining ballot secrecy. This represents the beginning of democratizing voting through verified, trustworthy, and inexpensive means.
Implementation Guide For the Future
For Individual Users
If you’re currently using SMS-based authentication, learn about Alternative Ways
to Avoid SIM Swap Attacks while transitioning to cryptographic authentication. Hardware security keys eliminate SIM swap vulnerability completely, providing mathematically proven protection.
Enable hardware security key support on email and financial accounts immediately. Hardware keys provide strongest protection because your private key never leaves the physical device. Purchase two keys—one for daily use and one as backup.
Install authenticator apps on your mobile device. App-based cryptographic authentication is free and provides strong security. Move away entirely from SMS codes. Use Google Authenticator, Authy, Microsoft Authenticator, or similar applications.
Use biometric authentication alongside cryptographic systems. Fingerprint and facial recognition provide convenience while maintaining security.
For Enterprise Organizations
Audit current authentication systems comprehensively. Identify password-exclusive systems and plan phased transition starting with highest-risk systems. Priority order: email systems, financial systems, healthcare data, then general applications.
Implement certificate-based authentication for critical infrastructure. Use hardware security modules to store root keys securely.
Plan post-quantum cryptography transition immediately. Early planning prevents chaos and allows thorough testing. Begin testing ML-KEM, ML-DSA, and SLH-DSA on non-production systems during 2026. Deploy hybrid systems starting in 2027. Plan complete RSA retirement by 2032.
Conclusion: The Inevitable Evolution
Cryptographic authentication is not the distant future—it’s the present reality. Organizations and individuals still relying primarily on passwords are genuinely vulnerable to modern attacks. Digital security now depends on mathematics, not secrets humans struggle to remember.
By 2030, most legitimate services will require cryptographic authentication. Passwords will disappear from normal consciousness. New users entering the workforce after 2028 may never interact with password-based authentication systems.
This transformation protects digital identity in ways passwords never could. Your data becomes mathematically secure, not just administratively protected. Your authentication becomes something you possess—like a hardware key—or something you are—like your fingerprint—not something you remember.
Every organization and individual should begin this transition immediately. The mathematics are sound. The security is proven. The future is cryptographic.