Phone Tracker is the best devices of the last and current century. It has brought a revolution in the business world. Nowadays, business professionals love to get their hands on mobile and tablet devices, and they also provide it to their workforce to engage with clients. Personal phones are prohibited in offices to interact with the clients via phone calls, messages, chats, voice messages, and voice calls.
However, numerous reasons have forced employers to use phone tracker on business-owned devices to keep tabs on employees during working hours. In this post, you can read why bosses need to track mobile devices provided to employees. We discuss the cell phone tracking software you need to know about the reasons to monitor and track business devices to the fullest.
Top Reasons to use Phone tracker for Employees
Following are reasons that you know that makes bosses think and use mobile trackers for their employees!
1. Cyberattacks
Cellphones these days are the most dangerous devices for business data, and every business uses cell phones for business activities. Therefore, phones are more likely to become the victim of online attacks. After every 40 seconds, a business firm faces cyberattacks on business devices. Phones are sensitive devices when it comes to protecting data. Therefore, a phone tracking app has become necessary for bosses to save business data and prevent cell phones from online attacks.
2. Scams and Fishy Activities
Cell phone scams and illegal activities can destroy your business to the fullest. Mobile devices are more likely to become the victim of scams activities online compare to PCs and computers. Bosses are more likely to install software on computing devices comparing phones that makes them vulnerable to email scams and malware attacks.
3. Less Productivity
Bosses are frustrated because of less productive activities on business-owned phones. Employees are more likely to use business phones for online dating, social messaging, and online shopping activities. Therefore, bosses need to keep tabs on employees during working hours, and you should know how to block and filter time-wasting activities on business phones to the fullest. The goldbricking of employees and less email marketing can cause issues for your business. So, use one of the best mobile trackers app to catch your employees involved in time-wasting activities during working hours.
4. Data sharing
Business-owned phones could breach your business data if your employee has become a rat in your company. They can sell the data of a business to a third party for lucrative reasons. So, the privacy of your business is necessary to make sure someone is not sharing it with anyone. It is possible to protect your business data on devices if you have installed a phone tracker app. It enables users to know what is happening on the phone, record live activities, and share them with you. Let’s discuss how to use the best cell phone monitoring app.
What is cell phone tracking software?
It is software that works as a phone tracke app on devices connected to cyberspace. It is the best monitoring application that monitors business devices and provides real-time results to business professionals. You can use it on your device to know what employees are doing during working hours. The application is hidden and easy to install on the target device. It has dozens of employee tracking tools that have made it the trademark of the mobile monitoring business. Let’s get to know about the powerful and trustworthy tool to spy on employees.
Top Features of Cell Phone Tracker
Here are the features that you activate on your business phones after successful installation, and you can protect your business to the fullest.
1. Capture screenshots
Employers can remotely capture screenshots on the target device, but you have to schedule screenshots via an online dashboard using a phone tracker.
2. Surround recording
The end-user can hack and track microphones of business phones to record and listen to the voice conversations, sounds, and arguments using the surround recorder app. You can download the data file by accessing the web control panel.
3. Screen recording
Employers can watch the real-time activities of employees on business smartphones running with Android and iOS. You can record live phone screen and record activities on screen and send to the web portal in short videos format.
4. Social media tracking
Users can read and monitor messaging app activity logs with the schedule. You can surveillance on instant messaging apps and send the messages, chats, media, and voice calls data to the web control panel.
5. GPS location Phone Tracker
A phone tracker is the best tool to monitor location history, real-time location and pinpoints the accuracy of the target device. Moreover, track the location of your employees without using GPS.
6. Read messages
Employers can read chat conversations and messages sent and received to clients with a schedule.
How does a phone tracker work on business devices?
Do you want to protect business phones from cyber-attacks, privacy breaching, and email scams? You need to install the best employee monitoring app that enables you to track employees. Let’s take a look at the steps given below to use a cell phone tracker.
- Step1: Get phone tracking software online subscription
First, you need to subscribe to cell phone monitoring software by visiting its official webpage. Further, check your email and get your hands on the password and ID.
- Step2: Possession of a business phone is necessary
You need to get physical access to the target device and start the process of installation. Moreover, activate the mobile tracker on the target device.
- Step3: Active the web control panel
You need to use the credentials and access the web control panel to access the features to monitor cellphones to the fullest.
Conclusion:
Bosses should keep an eye on business smartphone devices, and cell phone tracker empowers you to know every activity in real-time to the fullest. It has dozens of tools to track and monitor any cellphone device secretly.
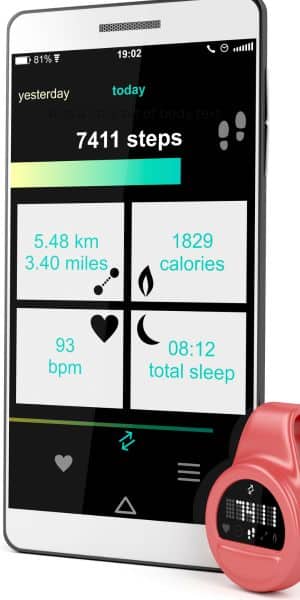
Check out: You Can Now Buy the Best Fitbit smartwatch