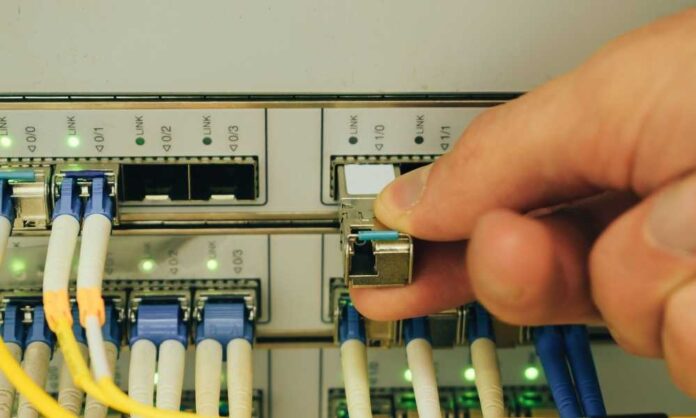
A Router is a physical device or a virtual appliance that helps forward data between connected systems on a computer network. It inspects the given data packet’s destination IP address, finds the best way for the package to reach its destination, and then forwards it.
It is a common type of gateway where two or more networks meet. Many people do not know that a router is not just about providing the internet; routers also have their Linex computers.
They are liable for routing internet traffic, giving encryption to guard our privacy, and connecting us to other devices. If you wish to learn more about configuring your router for the best possible settings, head over to our website at (https:routerlogin.app/10-90-90-90/) where we have curated hot-to guides and tutorials, just for you! Most of us hardly care to change our default passwords, but I suggest you change them once in a while for security purposes.
Usage of Rooting
Rooting, in a way, can make you the editor of your device. After rooting, you can do much stuff like installing the unsupported apps by google, unlocking the operating system of your device, replacing the firmware, adding custom ROM, and many more.
It helps to overcome the limitations of your device, but other than all the advantages, there can be certain disadvantages.
Rooting is not advised if one does not have the proper knowledge as it is a complex process.
Router Exploitation
Sometimes your router can be exploited; if by chance your router is hacked, criminals can use your network to attack other systems, steal your personal information, send you fake sites, and upload malware.
Pre-requisites
- An unrooted Android phone.
- Knowledge of the IP address of the target router.
- Termux app installed on your device. It’s a Linux Environment app that works without rooting or the setup. It can combine powerful terminal emulation with an extensive Linux package collection for you.
Unrooted Android Phones
It is commonly known by many that Android phones are unrooted by default. They have their security shield and limitations, which don’t let the user make any changes that will damage the hardware. These devices are the total opposite of rooted devices.
Steps to follow for Exploiting a Router Using an Unrooted Android Device:
Installing termux on your device.
You can search and find the app on the Google play store. If you have a Windows or Mac device, use this guide to install it on your Operating System. You need the android version 5.0 or above to access the app. An app is a command-line tool, so everything that you’ll do would be in commands.
Commands required
When you open the app for the first time (termux), you must make specific changes to install some packages. The commands to be given are written down below-
- apt update (for update termux)
- apt upgrade
- pkg install git (to install routersploit via GitHub)
- pkg install python (to run python scripts)
- pkg install python2
While using the commands, wait for one command to be executed entirely before typing the next one. After this, you will have all the required packages installed.
Installing Router sploit
As packet injection is not yet supported, you will need a framework like routersploit. Routersploit is a robust framework. It works just like Metasploit, and it helps you identify and exploit the router’s common vulnerabilities.
As all our packages are already installed, you now need to run the following command to install routersploit:-
Git clone https://github.com/reverse-shell/routersploit
Running Routersploit
Down below is a list of commands that you need to follow patiently.
- ls (it lists the names of files and folders present)
- cd routersploit (to change directory)
- pip2 install -r requirement.txt
- pip2 install requests
- pip install future
- python rsf.py (for running the python script)
rsf.py is the python script that contains the code to install routersploit.
After you have successfully installed routersploit, you need to type-
- show all (will show module options)
- use scanners/auto pawn (this will open the scanner and start scanning the target)
- If, in case you want to exploit nearby networks, consider
- Installing any of the apps available to locate the IP address.
- Show options (to see all available options on any module)
Now you need to set the target IP of the router you want to attack. Always make sure the device is connected to the network. Now you will need to enter the following command on your terminal window for doing the same-
- Set target <IP_address>
- Replace <IP_address> with the target IP address. You can enter show options again for rechecking if you want to check something.
- Now type run and press enter; after doing this, the module will display the list of vulnerabilities found for your target router.
Exploiting the found vulnerabilities
Once the scan is complete, you need to type use and then the path provided by auto-open to exploit.
Example- use <path>
All Done
WARNING
It is illegal to hack a router even if it is undefended. This article was made for educational purposes only and should not be used for personal purposes.