What is IP Spoofing?
Check out: How To Hide Your IP Address on iPhone?
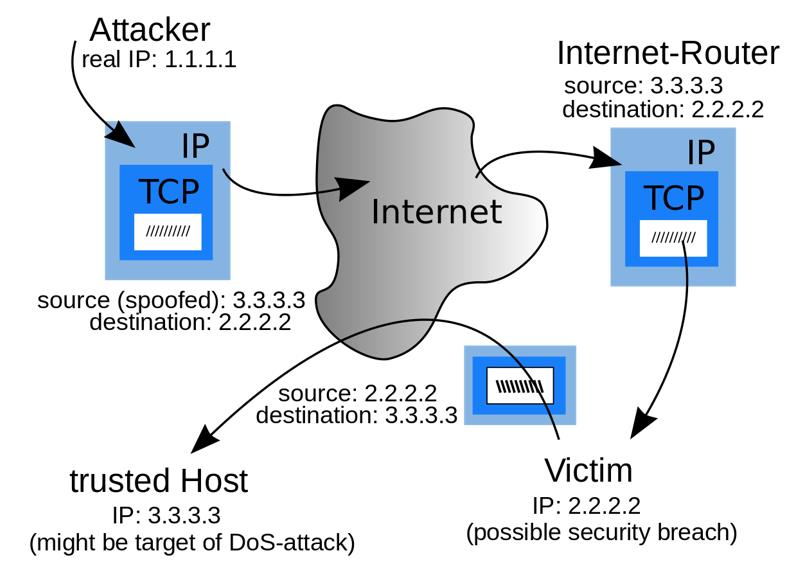
IP spoofing uses a modified source address to create an Internet package for encryption to impersonate another computer system. More often than not, the last goal would be to access other personal information. However, in some cases, attackers use the identity of the Internet access to commit crimes (perhaps offending and misrepresenting these individuals) or to commit outright denial or attack on the service.
IP Spoofing uses a process in which hackers create Internet Protocol (IP) that consists of modified source addresses. The source address is the address that consists of information about the sender. Hackers modify it because it hides the real identity of the sender. In short terms, they impersonate another computer with IP spoofing. Protecting your network against IP spoofing involves monitoring traffic for unusual source addresses to detect and prevent these deceptive tactics. IP spoofing can target a single device or surrounding infrastructure.
In a particular network, computers and other linked devices communicate via sending and receiving IP packets. It is the primary way of communication of devices. And when it is forged, the device is hacked. Now hackers can obtain any data from a particular server, which is a breach of user privacy.
1. Why Avoid IP Spoofing?
It is one of the many tools that is used for gaining unauthorized access to any computer. If someone wants to use a device or network without permission, IP Spoofing is most common. Mostly, they overwhelm the computer network with traffic and modify the packet header to look like it is coming from a trusted source, and a respected computer receives it because it occurs at the network level. Thus, there are no signs of tampering. Protecting your network against IP spoofing is crucial, as hackers use it to gain sensitive data, which they can use or sell to a third party. It also bypasses your IP address authentication.
As we know, the inside networks are safe, and outsiders are a threat; thus, it is a kind of security breach and looks like a family member but acts as a spy in the family and gives away all the family’s secrets. Now hackers can explore the system and use it as they want. It is most commonly used in Denial of service (DoS) attacks. It is challenging to filter because each spoofed packet appears to come from a different address and hides the trustworthy source of the attack.
2. The Dangers and Impact of IP Spoofing Attacks
It is considered a hazardous kind of attack because of the difficulty in detection. It allows hackers to stay concealed for a long time. This attack helps hackers gain access, and nobody can recognize it, and when the security system raises the alarm, enormous damage has already happened. It can bypass firewalls and other blockers and increase itself at a large scale, eventually doing more damage.
There are many types of IP Spoofing attacks. Some of the primary attacks are DDoS, Man in the middle attacks, Botnet attacks, etc.
How do you Protect Your Network Against IP Spoofing?
On the off chance that you wish to shield your framework from an IP spoofing assault, you first should be knowledgeable about the different manners by which you can recognize an assault in any case. A typical strategy for approaching this is to examine the framework to check for irregularities; for example, source IP tends not to match up with the organization’s remaining locations. Protecting your network against IP spoofing requires identifying these discrepancies early to prevent damage. The two most commonly utilized specific strategies are:
1. Steering Methods
Using switches empowers us to decide each IP address’ starting point focuses on the organization. Furthermore, they also help us get answers concerning the organization interface from which the IP address is hailing. Subsequently, they assist with keeping away from that load of parcels not intended to be gotten by a specific interface.
2. Non-Routing Methods
In the beginning, there are many ways, both aloof and dynamic, utilizing which one can decide if the parcel got is mock or not. Organization observing devices, like Netlog, can filter the bundles’ external interfaces being referred to. They likewise assist with recognizing IP parodying by examining cycle bookkeeping logs between frameworks present on the inward organization.
How Might You Prevent IP Spoofing?
- The most normally took on rehearses for forestalling and controlling satirizing assaults are.
- We are utilizing a confirmation framework dependent on the exchanging of keys like IP.
- Hindering private IP addresses by utilizing ACL on downstream interfaces.
- Oppressing both inbound and outbound traffic to sifting.
- Relocating the web application to IPv6 accordingly forestalls satirizing through its execution of verification and encryption steps.
Finally, it is necessary to protect your network against IP spoofing to maintain the integrity and safety of your digital infrastructure. This form of cyber attack can be difficult to detect severe hazards and find out those serious hazards that include unauthorized access to sensitive data and the possibility of massive damage. You can significantly reduce risks, understanding how IP Spoofing works and using strong safety measures, such as unusual sources monitor the address and advanced filtering techniques. To take active steps, such as using IP certification and switching to IPV6, ensuring that your network is safe and flexible against these dangerous attacks.
Check out: What are 5 Huge Advantages of Cloud Security Services?