As Android is now the most popular operating system globally, it’s just as important to secure Android applications as PCs and servers. Mobile penetration testing can help find security vulnerabilities that could be costly for your business and customers if exploited. An Android penetration test consists of several phases that are briefly described below. The Android application security is also covered with the most popular open-source and commercial tools used for mobile penetration testing. This blog post will help you understand how to get started with mobile pen testing for Android applications, becoming increasingly important as Android is now the most popular mobile OS in the world.
Why is Mobile Penetration Testing important?
It’s recommended to perform a mobile pen test on any app that handles customer data, like finance applications, payment gateways, or games with online leaderboards. Mobile security bugs can cost your business money and damage trust in your brand. A recent study found that hackers are increasingly interested in hacking Android apps because of the high number of vulnerabilities discovered compared to iOS apps. These techniques also allow attackers to bypass enterprise protection solutions such as MDM, making Android smartphones an attractive target for non-criminals looking for ways to access sensitive company information without being detected by traditional antivirus software.
What are Mobile Penetration Testing phases?
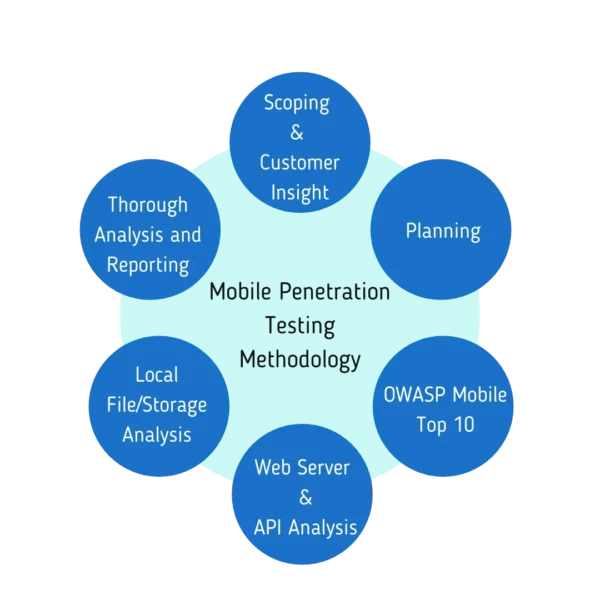
Each phase consists of several activities conducted with different techniques depending on the target environment (e.g., Google Play Store vs. internal servers). During your project life cycle, all these steps may become necessary to achieve successful results. The following text only provides an overview without getting into too many details as each project has unique requirements which must be prioritized according to the business and security goals. Android Penetration Testing.
Android application testing is a compulsory part of mobile pen-testing. The scope can range from analyzing Google Play Store applications for known vulnerabilities, identifying new back doors into your network, verifying compliance with data protection regulations such as GDPR or PCI DSS, etc. It’s also worth mentioning that Android app penetration testing should not be treated in isolation since it’s highly dependent on other activities carried out earlier during the information gathering phase (e.g., foot-printing).
How can Mobile Penetration Testing be helpful to my business?
Android penetration testing is becoming increasingly important as Android has surpassed Windows in popularity for mobile operating systems, so it’s worth understanding how an experienced Android pen tester might compromise your app security. If Android application vulnerabilities are exploited, it may lead to loss of sensitive data, or there could even be a possibility that the attacker would gain access into critical network infrastructure, which would have serious consequences on both your company and customers.
What are some key features of open source tools used for Android Pentesting?
Android penetration testing is becoming increasingly important as Android has surpassed Windows in popularity for mobile operating systems. The Android pen test consists of several phases, including reconnaissance, scanning, and exploitation.
Drozer (previously known as Mercury) – an exploitation framework built around communication over RPC channels with support for multiple architectures, including ARM, x86, and MIPS. Android penetration testing helps identify vulnerabilities, data leakage, or gaining access into the critical network infrastructure.
Android Debug Bridge (ADB) – ADB is an Android command-line tool that facilitates interaction with an emulator instance or Android-powered device. ADB is a powerful tool and can help Android penetration testers execute tasks such as side-loading applications, running shell commands remotely, injecting input events, etc.
Android Debug Bridge can be used in Android penetration testing for accessing Android shells. In Android, the ADB is a native debugging protocol that allows you to communicate with an emulator instance or connected Android device over a USB connection from a host machine via command line.
Android Tamer – A security-oriented Android application with the main purpose of helping pentesters and bug hunters perform Android security tests on Android applications. Android Tamer has different functions that can prove to be extremely valuable during an Android penetration testing engagement.
What are some Android Penetration Testing Tools which can be used?
There are several Android pen-testing tools available both at no cost and in commercial versions (my personal preference is Drozer). Some popular open-source Android penetration testing frameworks include:
- AndroRat – Android application RAT(Remote Administration Tool) to control a victim’s phone from console or PC over WiFi/Bluetooth by sending simple bash commands such as “SMS Command” or “Keylogger.”
- DroidBox – An interactive tool that helps analyze the behavior of Android applications in a sandbox environment. DroidBox is an Android application dynamic analysis tool that allows you to run Android applications inside a controlled environment and monitor their behavior.
- Drozer – A security assessment framework for Android that makes it easy to identify security vulnerabilities in Android apps, assess the risk they pose, and take appropriate action with just a few simple clicks.
- Fiddler – An interactive debugging proxy for any website or app where you can inspect traffic as it passes through your device.
Conclusion
Mobile penetration testing becomes increasingly important as Android has surpassed Windows in popularity for mobile operating systems, so it’s worth understanding how an experienced Android pen tester might compromise your app security. If Android application vulnerabilities are exploited, it may lead to loss of sensitive data, or there could even be a possibility that the attacker would gain access into critical network infrastructure.
which would have serious consequences on both your company and customers. Find open-source tools that help you understand how your application might be compromised by an expert Android tester, run tests with powerful modules including Android reverse engineering, patching binaries on the fly, and injecting custom code into processes for privilege-escalation purposes.
Check out: 6 Website Penetration Tools You Can Utilize