Firewall is an essential cybersecurity hardware or software to protect computer networks from illegal cyber attacks, unauthorized entry and other malicious online risks. Firewalls are stop gates that you sit between yourself and an external and potentially dangerous connection and do some periodic checking. Firewalls operate on the principle of managing security rules in advance, allowing incursions to be prevented from taking place. Before we get into firewalls in general, we’ll get into what is hardware firewall and how these devices can be beneficial to keeping your network as secure as possible.
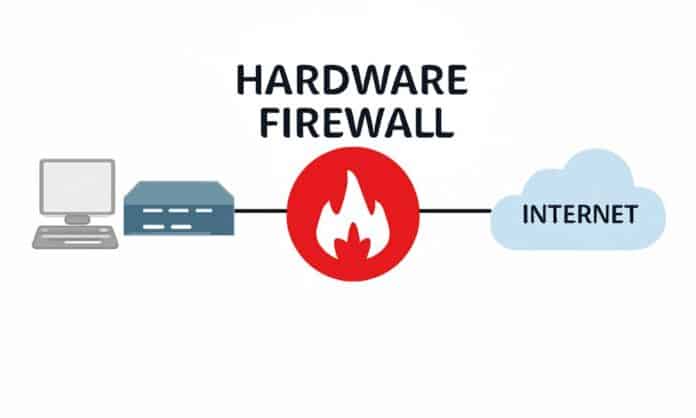
A hardware firewall is a device that serves as a defense between the local network (LAN) and the Internet (WAN), effectively protecting a business’s network from unwanted access. Firewalls may be either a separate device or they could be a software-based program located on the computer. Today, most networks will have both a hardware and software firewall and each has its own unique networking task to perform. When it comes to deciding on hardware or software firewalls, one size does not fit all — the type that suits one company may be ill-suited to another’s needs.
What is Hardware Firewall?
A Hardware Firewall is a device or a group of physical devices that serve as front-line security for a computer network. A router, for example, is a very simple hardware Firewall that is widely found in most households with Wi-Fi Fibernet connections.
A basic hardware solution A firewall is a physical device that serves as a buffer between a computer or an organization’s computer network and the outside network or the internet, shielding them from unauthorized users with malicious intent.
Different Types of Hardware Firewalls
There are several manufacturers of firewall hardware. The organization’s needs determine the type of hardware and vendor chosen.
Until finalizing the selection of a firewall, several considerations should be taken into account.
- The security level required for the network of computers.
- The company’s main operational area. If it is involved in the defense business, it would need the most sophisticated firewall possible to plug in any data breach relevant to national security.
- The amount of budget available for the implementation of the Firewall.
- The required human resources for maintaining the firewall.
- Reliability and after-sales help the vendors’ credibility.
- The availability of upgrades regularly.
Hardware Firewalls are available in several configurations. Here is a list of hardware firewalls from the most popular major vendors that cater to businesses looking to protect their data from leakage and theft.
- CISCO PIX Firewall.
- Checkpoint.
- Sun’s iForce VPN/Firewall.
- Fortinet.
- Watchguard.
- Sophos.
- Forcepoint.
- Juniper SRX.
- D-Link and Linksys for home systems.
- Sidewinder G2.
- Sonic WALL.
- Palo Alto.
- Fortinet.
- Barracuda NEXTGEN Firewall.
Best Hardware Firewall
Now we’ll take a look at the best hardware firewalls for small businesses.
The following are some of the best HD Firewalls for small businesses:
- A basic router is the Ubiquiti Edge Router.
- The best corporate firewall is CISCO NGFW.
- The perfect one for a home business is Firewalla.
- The one for data-dependent organizations is SonicWALL.
- The best overall Firewall is Fortinet.
What is Hardware Firewall, and how do it work?
For the uninitiated, the issue of how the firewalls work requires some clarification. A hardware firewall usually comes with proprietary software pre-installed at the source as a single device. This makes the selection less difficult since no separate compatible software package must be selected to run the hardware. Although some hardware Firewalls operate with standard operating systems such as Linux, most Firewalls come with their own proprietary operating systems specifically designed and optimized to run the program. This is a significant security benefit because general operating systems could contain vulnerabilities that hackers can exploit to access the system’s defenses.
Benefits of Hardware Firewall
For information protection, a hardware firewall relies on the hardware to perform the data package filtering operation. The significant advantages of a hardware firewall are:
- One of the most important benefits of a hardware firewall is that it has lower latency or takes to process a packet.
- Another big gain is that it has improved bandwidth or the capacity to handle more data packets per second.
- It governs the information-based data traffic on a set of guidelines.
- Since the Firewall program may be located outside the server, it can free up additional server resources.
- A hardware firewall can run a VPN link. This adds encryption and confidentiality to the network at a higher level. This allows approved users to be provided with access, even while traveling or working from outside.
Key Features to Consider
Some of the firewall hardware features that need to be considered when choosing an organization’s firewall are:
- VPN: This is important if you require an extremely secure firewall. VPN gives Site-to-site encryption. This will make even the hackers invisible to the user as he will only be seen as using a VPN server.
- High availability: in the event of the primary firewall breaking down, with the secondary firewall taking over the defense. This is important for organizations that depend heavily on data.
- Packet Filtering: For smaller enterprises, a router would suffice.
- Stateful inspection: For medium-sized businesses, firewalls that look into the data packets’ information are needed.
- Proxy Firewall: This masks the user’s source and offers anonymity.
- Host-based Firewall: Firewalls that are hosted on a single device are known as host-based firewalls. Each one would need to provide an individual firewall for more systems.
- Network Firewalls: For a network with many machines, this is necessary.
- Enterprise Firewalls: These integrate most of the advanced features required for top-end security in large companies, such as VPN.
What is the Key Function?
By now, you should have a reasonable idea of what a hardware firewall is and what it does. Some of the precautions it provides are.
- Every data packet accessing the network must first pass through the Firewall, which functions as a buffer between internal and external systems.
- A Hardware Firewall prevents remote access and hacking.
- It safeguards data by preventing unauthorized users and suspicious data from accessing the system.
- It operates on a set of rules laid down for information security by the organization.
- This guarantees better confidentiality and protection.
- It defends against Trojans.
- A router, like a network-based firewall, can protect several systems connected to the server.
Conclusion: What is Hardware Firewall?
Hardware Firewall A hardware firewall is a stand alone device or set of devices that is normally installed in front of personal computers or a network of personal computers to protect them from threats that jump up from information and data leaks. It operates by blocking the attempts to access data by unauthorized users. So, what in the blazes is a hardware firewall?
Serve as physical block to disrupt the connection between network and threats in network world, guarantee the most insane level of security of both your personal space and cooperate network. And large corporate data breaches still happen, despite a lot of money being thrown at the issue and committed teams driving the effort! This highlights the need to realise and enforce a decent firewall protection. At the end of the day ongoing vigilance and screening, automated updates and monitoring systems are required to avoid the complacency blind-spot and to guard against potential incursions.