XML-RPC is actually a remote procedure call protocol that allows anyone to disturb your WordPress website remotely. In other words, anyone like a hacker can manage your website without logging in manually through the standard “wp-login.php” URL page. It’s extensively used by some plugins, most famously by the Jetpack plugin. However, the word “XML-RPC” has a bad reputation. In this tutorial, I will explain WordPress XML-RPC and how to stop the XML-RPC DDoS attacks on your WordPress website.
Now the question is, how to check this problem If you are not already facing this. So you can check if XML-RPC is already Enabled to protect Your WordPress website from DDoS attacks.
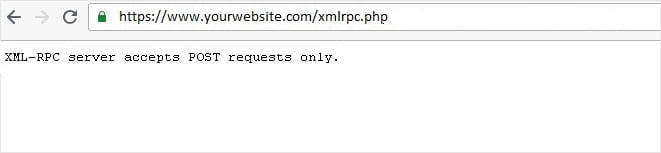
A quick way to check if your site is defenseless is to visit the following URL from a browser:
Type in your browser https://www.yourwebsite.com/xmlrpc.php (replace www.yourwebsite.com with your own domain name)
If it is enabled, you will get a response like that “XML-RPC server accepts POST requests only.”
The Dangers and Benefits of XML-RPC
There’s been a lot of back and forth in the WordPress security community about XML-RPC. There are mostly two concerns:
- XML-RPC can be used to stop DDoS attacks (Distributed Denial of Service) a site
- It can be used to try username/password combinations to access your website frequently.
Here are a few steps and ways to avoid that kind of attack on your website against XML-RPC – starting from the lightest touch to the heaviest.
Check out: How to change WordPress Website’s default Login URL with a Plugin
Method 1: Disable Pingbacks
This is a method that uses your server as an unwitting participant in an attack against another server. In this case, someone tells your site, “this URL is linked to your blog!” And then, your site replies with a “pingback” to that URL.
But there is no proof that the URL actually did link back to you. Do this with hundreds of vulnerable WordPress sites, and you have a DDoS (Distributed Denial of Service) attacks on your hands! The most simple and easiest method to avoid your site from being used in this manner is to add the following code to your theme’s functions.php:
function stop_pings ($vectors) {
unset( $vectors['pingback.ping'] );
return $vectors;
}
add_filter( 'xmlrpc_methods', 'stop_pings');
Method 2: Prevent All Authentication Requests via XML-RPC
This second method regulates if you want to allow “XML-RPC” methods that authenticate users. For example, publishing content through e-mail. The site will receive your e-mail, allow you via XML-RPC, and then publish it if the credentials match.
Many people are uncomfortable with XML-RPC’s ability to take in random calls like this. It’s what led to hundreds or thousands of authentication attempts in the first place. WordPress has also addressed this specific hacking method; you can turn it off by using a shortcode in your theme’s functions.php file.
add_filter('xmlrpc_enabled','__return_false');
You must know that this is not a similar method as the first I mentioned. This shortcode only restricts the authentication methods and leaves all others untouched, like pingbacks.
Method 3: Disable Access to xmlrpc.php
This method is the most extreme level of blocking that completely restricts all XML-RPC functionality. So you need to edit the “.htaccess” file at the root of your WordPress website directory (www.yourwebsite.com/.htaccess). You need to add the following code in the mentioned file.
<files xmlrpc.php> Order allow, deny Deny from all </files>
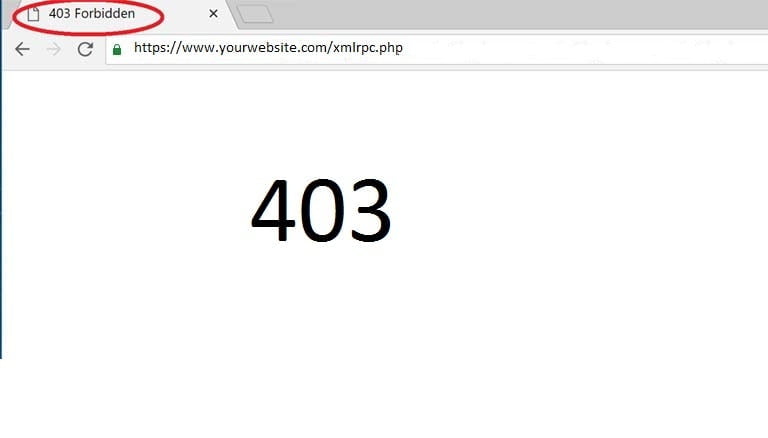
Now with the above denial rules in effect, trying to access xmlrpc.php will be met with the following page:
That’s all; you have successfully disabled XML-RPC altogether on your WordPress Site.