Do you want free Firewall Software For Windows to secure your device or computer? Read this analysis to pick the best security free Firewall Software For Windows:
According to a recent MaketsandMarkets.com report, the Network Security Firewall Market is expected to increase to 5.3 billion dollars by 2023. There are many reasons why the firewall market is rising.
Today, however, most organizations are looking for Firewall Software For Windows to secure their confidential or critical data.
Firewall Security: An Overview
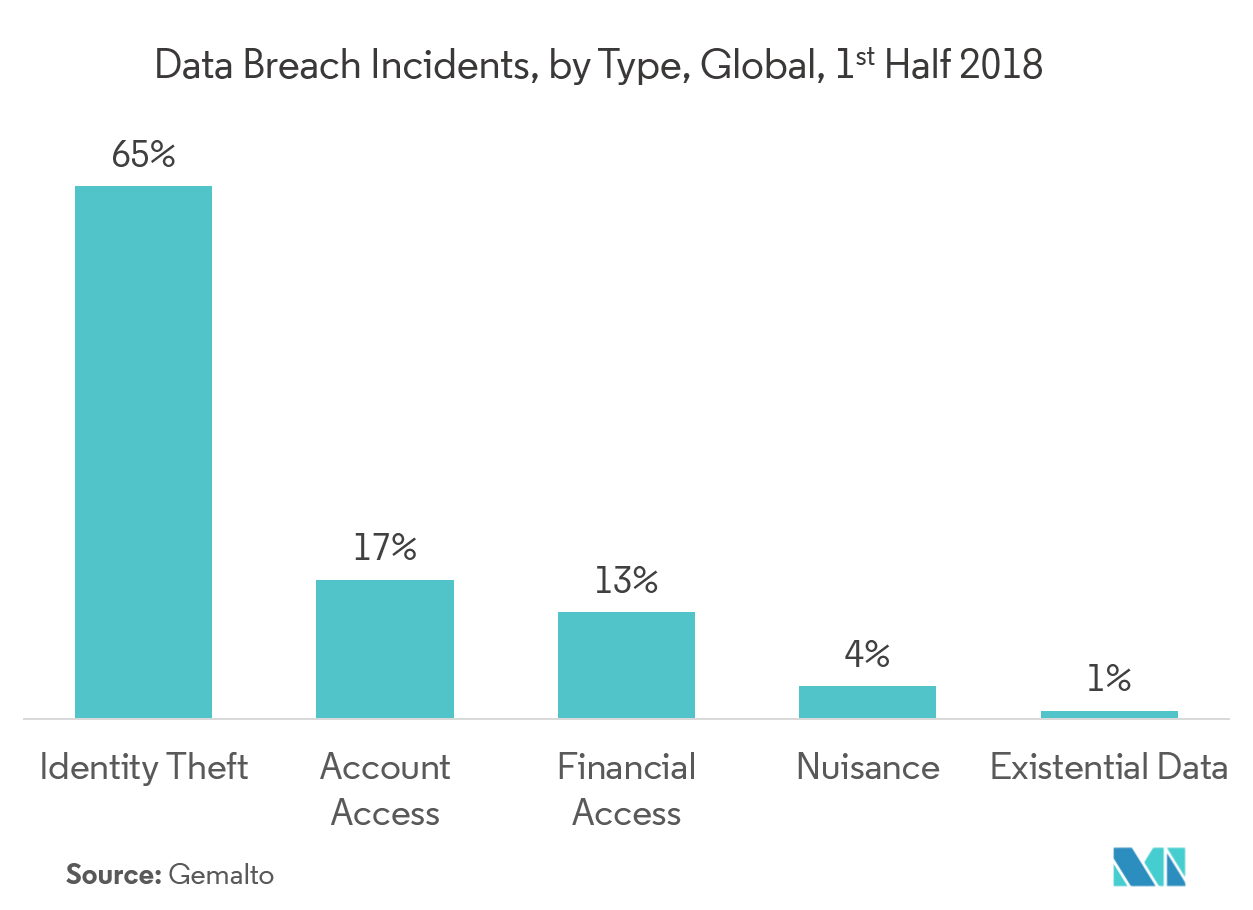
The following infographic shows the types of data breaches that companies are most concerned with and seek firewall protection:
Image: mordorintelligence.com
Looking at the diagram above, we can see that identity theft is by far the most significant concern of companies seeking protection against cyber and firewalls today. But what makes the security of firewalls so critical or ‘so useful’ in other words?
Perhaps the best way to find this out is by reacting to our questions about the next section’s firewall program.
Check out: What is a Hardware Firewall? Everything You Need to Know
Most common Questions About Firewall
The most popular questions about firewalls are described below.
1. What is a firewall?
A security shield or buffer from unauthorized access by a private network, a firewall secures Internet devices or other networks such as a local area network (LAN).
The aim of getting a Firewall Software For Windows pc, phone, or tablet is to protect users from online or other linked network data-based malware risks.
Data transfers between your PC and servers and routers in cyberspace. This data, transmitted via packets, are monitored via a firewall to detect and block unwanted traffic.
The firewall software does this by checking the data packets for the rules collection. If the data packets adhere to these guidelines, the firewalls are approved. If the rules are not followed, the Firewall will reject or block them.
Today, firewalls help secure computers and other wired devices worldwide, whether they belong to individual users, big companies, or the government.
2. How does Firewall Software Work?
Answer: Firewalls function simply by monitoring information traffic to accept or allow ‘good data’ while refusing or blocking ‘bad or harmful information.’ However, if we go into the specifics, the firewall software uses three methods or combinations to control traffic flowing inside and outside the network.
The three ways a firewall prevents a PC, tablet, or other computer are:
- Packet Filtering
- Proxy Service
- Stateful Inspection
Involving the use of a pre-defined set of rules for filtering, packet filtering is the most basic form of security against firewalls. The Firewall Software For Windows does not allow a data packet to reach a network if the filters are flagged. All data packets are discarded, except those made by filters.
A firewall proxy can collect information from the Internet and then send it to the requesting device. A software or application that functions as an intermediary between systems. The application layer of the Firewall is where the Firewall Proxy Servers operate.
It is compulsory to use a proxy to perform the session on both ends of a connection. A process representing a service running on the host end is generated and run on the proxy server’s Firewall. Consequently, all data transmission for an operation is centralized for firewall scanning.
The third and final firewall approach for securing a computer or system is a thorough inspection. The most modern, state-of-the-art firewall scanning holds each link’s data attribute in a database during the session.
These attributes include essential details such as link port and IP addresses and the order in which the data packets are transmitted, collectively known as the ‘state’ of the connection. The relevant information in the database is compared to the firewall data.
The Firewall allows the data to move if the comparison results in a good match. Otherwise, the entry of the data packet or information is rejected.
3. What are the Different types of Firewall software?
There are two basic Firewall types, i.e., Appliance Firewalls and Client-based Firewalls. Customer-based firewall software is mounted on a device to monitor traffic on that specific device.
On the other hand, the appliance firewall is a variant of the Firewall that involves a system positioned between a user’s network and an external network, such as the Internet.
Often, devices that share the same network or internet connection are used for network environments with multiple devices. On the other hand, customer or firewall software is ideally suited to customize security levels and configure firewall permissions for individual users or a group of users.
4. How do Firewalls protect us from Hackers?
Firewalls defend against hackers by blocking access via Wi-Fi and the Internet to your PC.
Hackers use keylogging software and Trojan viruses to access your PC and steal sensitive data such as your browsing records, bank details, passwords, and other such stuff, to record your sessions and track your keystrokes. We mean by keystrokes what you enter on your PC or other devices.
Hackers can carry out illegal activities even without your knowledge using your computer. The good news is that firewalls will contribute to stopping them.
Check out: Difference Between Hardware Firewall and Software Firewall
How will firewalls protect your computer against hackers? If all unauthorized connections to your device are blocked.
Furthermore, a firewall helps you to choose programs that can access the Internet on your computer. This means that you never link unknowingly to the Internet. This prevents hackers and other cybercriminals from accessing your device through a Wi-Fi or Internet connection.
5. Can a Firewall be Compromised (Hacked)?
It’s a rare thing to hack a firewall. If Firewall Software For Windows is not correctly tuned, cybercriminals can easily hack it. While a firewall is intended to protect your device from hackers, system protection can be affected if you improperly configure or manage a firewall.
No matter how compelling your firewall security is, hackers will circumvent the Firewall if vulnerabilities exist in firewall-protected systems and applications. For example, Windows contains many vulnerabilities that attackers may use to access your device.
They have to persuade you to visit an infected website. That makes it critical to have anti-virus and anti-malware software installed alongside the firewall software on your PC or systems.
Make sure that the current update of both software and operating systems is patched. If you do this, you have a slight risk that a hacker will access your device.
6. How to choose the right Firewall Software?
It can be challenging to pick the right firewall software for your needs with so many choices. However, if you consider the following parameters to determine the best free Firewall, you are likely to make the right decision:
- Protection and prevention from threats.
- Visibility and control of your applications.
- Streamline security infrastructure.
- Real-time alerts
- Excellent customer support.
The above list is by no means complete, and there is a range of other factors to consider when selecting the best free firewall software.
List Of The Best Free Firewall Software
- SolarWinds Network Firewall Security Management
- System Mechanic Ultimate Defense
- Norton
- LifeLock
- ZoneAlarm
- Comodo Firewall
- TinyWall
- Netdefender
- Glasswire
- PeerBlock
- AVS Firewall
- OpenDNS Home
- Privatefirewall